Security Considerations in System on a Chip Design and Implementation
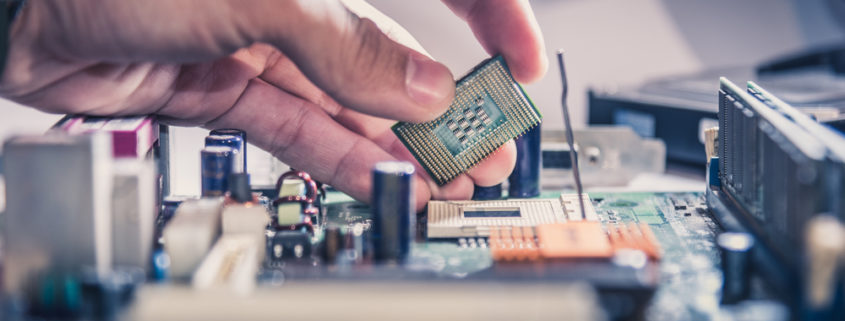
As the demand for integrated and compact electronic systems continues to grow, System on a Chip (SoC) designs have become a cornerstone of modern microsystems. SoCs integrate multiple functions into a single chip, offering efficiency and performance. However, the increased complexity of these systems also brings forth a heightened need for security. In this article, we delve into the critical security considerations that must be addressed in SoC design and implementation.
Threat Landscape and Vulnerabilities
Understanding the evolving threat landscape and potential vulnerabilities is a vital starting point in securing SoC designs. Here are some key factors to consider:
System on a Chip Hardware and Software Attacks
SoC security should address both hardware and software vulnerabilities. Hardware attacks can involve physical tampering, reverse engineering, or side-channel attacks. Software threats may include malware, exploits, and unauthorized access to firmware.
Supply Chain Risks
The SoC supply chain can be susceptible to attacks. Malicious actors may attempt to insert vulnerabilities or backdoors during the manufacturing or distribution processes. Ensuring the integrity of the supply chain is crucial.
Data Privacy
SoCs often handle sensitive data in applications like IoT devices, medical devices, and automotive systems. Protecting data at rest and in transit is a priority. Encryption and secure key management are essential components of data privacy.
Authentication and Authorization
Unauthorized access to SoC systems can lead to breaches. Strong authentication and authorization mechanisms are critical for ensuring that only authorized users or devices can access and control the SoC.
Firmware Security
The security of firmware is paramount, as it controls the behavior of the SoC. It should be protected from tampering and unauthorized updates. Secure boot processes and firmware encryption help safeguard against attacks on the firmware.
Security Measures in System on a Chip Design and Implementation
Securing SoCs requires a combination of hardware and software measures throughout the design and implementation phases. Here are some fundamental security practices to integrate:
Secure Boot
Implement secure boot processes to ensure that the SoC only starts up with trusted firmware and software. This prevents the execution of malicious code during boot-up.
Hardware Security Modules (HSMs)
Incorporate hardware security modules within the SoC. These dedicated hardware components provide secure key storage, cryptographic operations, and authentication features.
Isolation and Segmentation
Use hardware-based isolation to separate critical components from less trusted parts of the system. This helps contain and mitigate potential breaches.
Regular Updates and Patch Management
Design SoCs with the ability to receive and install software updates securely. Regular updates are essential to address newly discovered vulnerabilities and improve system security.
Secure Communication
Employ encryption and secure communication protocols to protect data in transit. This is crucial for IoT and network-connected SoCs that exchange data with external systems.
Monitoring and Intrusion Detection
Implement mechanisms for monitoring system behavior and detecting potential intrusions. Real-time alerts and responses can help mitigate security incidents promptly.
Secure Debugging Interfaces
Secure debugging interfaces and provide them with access controls to prevent unauthorized access to the SoC during development and testing.
Security Testing and Validation
Conduct thorough security testing and validation at every stage of SoC development. This includes vulnerability assessments, penetration testing, and code analysis.
Lifecycle Management
Plan for the entire lifecycle of the SoC, including end-of-life considerations. Ensure that the SoC can be securely decommissioned or updated as needed.
In conclusion, as SoCs continue to play a pivotal role in microsystems, securing these complex integrated systems becomes imperative. A holistic approach to security, spanning from threat assessment to design, implementation, and ongoing maintenance, is necessary to safeguard against emerging threats and vulnerabilities. By addressing security considerations at every stage of SoC development, microsystems companies can deliver reliable, resilient, and trusted solutions to their customers and partners.
Learn more about Linear MicroSystems by clicking here!
Linear MicroSystems, Inc. is proud to offer its services worldwide as well as the surrounding areas and cities around our Headquarters in Irvine, CA: Mission Viejo, Laguna Niguel, Huntington Beach, Santa Ana, Fountain Valley, Anaheim, Orange County, Fullerton, and Los Angeles.